Company Details
worcester-public-library
99
452
51912
mywpl.org
0
WOR_1482622
In-progress

Worcester Public Library Company CyberSecurity Posture
mywpl.orgVISION The Worcester Public Library will be a welcoming destination and the leading provider of resources to inform, enlighten and enrich our diverse community. MISSION The Worcester Public Library serves as a gathering place that actively promotes the free exchange of ideas in our democratic society. The Library makes information and services available to all people while fostering intellectual freedom, protecting privacy, encouraging personal growth and enrichment, and celebrating our diverse community heritage.
Company Details
worcester-public-library
99
452
51912
mywpl.org
0
WOR_1482622
In-progress
Between 750 and 799

 WPL Global Score (TPRM)
WPL Global Score (TPRM)XXXX



No incidents recorded for Worcester Public Library in 2025.
No incidents recorded for Worcester Public Library in 2025.
No incidents recorded for Worcester Public Library in 2025.
WPL cyber incidents detection timeline including parent company and subsidiaries

VISION The Worcester Public Library will be a welcoming destination and the leading provider of resources to inform, enlighten and enrich our diverse community. MISSION The Worcester Public Library serves as a gathering place that actively promotes the free exchange of ideas in our democratic society. The Library makes information and services available to all people while fostering intellectual freedom, protecting privacy, encouraging personal growth and enrichment, and celebrating our diverse community heritage.


Founded in 1901, the Pennsylvania Library Association (PaLA) is the state's oldest and most diverse professional library organization serving libraries, library employees, library trustees, and Friends of the Library groups. PaLA represents more than 1,500 personal, institutional, and commercial me

Freeport Memorial Library provides extensive Career, Education and Computer programs serving the community. Services include ESL and GED classes, Career and Exam Preparation Databases, Career Counseling, Civil Service Announcements and test books and various career support periodicals. Computer S

The library's mission is to provide access to information, materials, and services for community residents of all ages. The library's vision is to become the heart of our community by providing: -A safe, fun and engaging facility for community members to visit; -Library materials and services that

Toronto Public Library is the world's busiest urban public library system, with more than 46 million annual visits to our branches and online. We empower Torontonians to thrive in the digital age and knowledge economy through easy access to technology, lifelong learning, and diverse cultural and lei
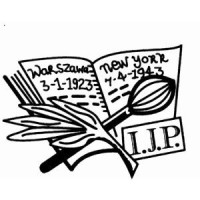
The Pilsudski Institute of America is one of the most outstanding Polish institutions outside of Poland. It has earned that designation through its invaluable collection of documents on the modern history of Poland, and its distinguished record of defending historical truth about Poland against succ

Washington County Library has served the residents of Washington County since 1966. Our mission is to inspire curiosity, champion innovation, and spark opportunity through the materials, programs, and resources we provide. Each year, we lend more than two million print and electronic books, CDs, D
.png)
The College of the Holy Cross in Worcester has launched a $10000 micro-grant pilot program aimed at strengthening the college's...
Holy Cross has launched its Worcester Pillar Micro-Grant Pilot Program, a new initiative designed to deepen the College's engagement with...
The Worcester Public Library first established a bookmobile program on Nov. 18, 1940, when librarians loaded a truck with 2700 books.
Narrowing the fields for city councilor-at-large and District E School Committee representative.
Concerts, candlemaking, yoga, and comedy are just some of the local Valentine's Day events happening in February.
Explore cybersecurity salaries in Worcester, Massachusetts. Learn what influences earnings and discover top employers for cybersecurity...
Latest in a series of stories on the people whose names are attached to Worcester schools, streets and parks. For a decade after college,...
ComputerVault moved from Marlborough to downtown Worcester, picked up the keys for One Mercantile and celebrated the move into the Mercantile Center on...
The Boston Public Library is working to restore its digital services after being hit by a cybersecurity attack. Read more on Boston.com.

Explore insights on cybersecurity incidents, risk posture, and Rankiteo's assessments.
The official website of Worcester Public Library is http://www.mywpl.org.
According to Rankiteo, Worcester Public Library’s AI-generated cybersecurity score is 755, reflecting their Fair security posture.
According to Rankiteo, Worcester Public Library currently holds 0 security badges, indicating that no recognized compliance certifications are currently verified for the organization.
According to Rankiteo, Worcester Public Library is not certified under SOC 2 Type 1.
According to Rankiteo, Worcester Public Library does not hold a SOC 2 Type 2 certification.
According to Rankiteo, Worcester Public Library is not listed as GDPR compliant.
According to Rankiteo, Worcester Public Library does not currently maintain PCI DSS compliance.
According to Rankiteo, Worcester Public Library is not compliant with HIPAA regulations.
According to Rankiteo,Worcester Public Library is not certified under ISO 27001, indicating the absence of a formally recognized information security management framework.
Worcester Public Library operates primarily in the Libraries industry.
Worcester Public Library employs approximately 99 people worldwide.
Worcester Public Library presently has no subsidiaries across any sectors.
Worcester Public Library’s official LinkedIn profile has approximately 452 followers.
Worcester Public Library is classified under the NAICS code 51912, which corresponds to Libraries and Archives.
No, Worcester Public Library does not have a profile on Crunchbase.
Yes, Worcester Public Library maintains an official LinkedIn profile, which is actively utilized for branding and talent engagement, which can be accessed here: https://www.linkedin.com/company/worcester-public-library.
As of November 28, 2025, Rankiteo reports that Worcester Public Library has not experienced any cybersecurity incidents.
Worcester Public Library has an estimated 1,268 peer or competitor companies worldwide.
Total Incidents: According to Rankiteo, Worcester Public Library has faced 0 incidents in the past.
Incident Types: The types of cybersecurity incidents that have occurred include .
.png)
Angular is a development platform for building mobile and desktop web applications using TypeScript/JavaScript and other languages. Prior to versions 19.2.16, 20.3.14, and 21.0.1, there is a XSRF token leakage via protocol-relative URLs in angular HTTP clients. The vulnerability is a Credential Leak by App Logic that leads to the unauthorized disclosure of the Cross-Site Request Forgery (XSRF) token to an attacker-controlled domain. Angular's HttpClient has a built-in XSRF protection mechanism that works by checking if a request URL starts with a protocol (http:// or https://) to determine if it is cross-origin. If the URL starts with protocol-relative URL (//), it is incorrectly treated as a same-origin request, and the XSRF token is automatically added to the X-XSRF-TOKEN header. This issue has been patched in versions 19.2.16, 20.3.14, and 21.0.1. A workaround for this issue involves avoiding using protocol-relative URLs (URLs starting with //) in HttpClient requests. All backend communication URLs should be hardcoded as relative paths (starting with a single /) or fully qualified, trusted absolute URLs.
Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. An Uncontrolled Recursion vulnerability in node-forge versions 1.3.1 and below enables remote, unauthenticated attackers to craft deep ASN.1 structures that trigger unbounded recursive parsing. This leads to a Denial-of-Service (DoS) via stack exhaustion when parsing untrusted DER inputs. This issue has been patched in version 1.3.2.
Forge (also called `node-forge`) is a native implementation of Transport Layer Security in JavaScript. An Integer Overflow vulnerability in node-forge versions 1.3.1 and below enables remote, unauthenticated attackers to craft ASN.1 structures containing OIDs with oversized arcs. These arcs may be decoded as smaller, trusted OIDs due to 32-bit bitwise truncation, enabling the bypass of downstream OID-based security decisions. This issue has been patched in version 1.3.2.
Suricata is a network IDS, IPS and NSM engine developed by the OISF (Open Information Security Foundation) and the Suricata community. Prior to versions 7.0.13 and 8.0.2, working with large buffers in Lua scripts can lead to a stack overflow. Users of Lua rules and output scripts may be affected when working with large buffers. This includes a rule passing a large buffer to a Lua script. This issue has been patched in versions 7.0.13 and 8.0.2. A workaround for this issue involves disabling Lua rules and output scripts, or making sure limits, such as stream.depth.reassembly and HTTP response body limits (response-body-limit), are set to less than half the stack size.
Suricata is a network IDS, IPS and NSM engine developed by the OISF (Open Information Security Foundation) and the Suricata community. In versions from 8.0.0 to before 8.0.2, a NULL dereference can occur when the entropy keyword is used in conjunction with base64_data. This issue has been patched in version 8.0.2. A workaround involves disabling rules that use entropy in conjunction with base64_data.

Get company history
















Every week, Rankiteo analyzes billions of signals to give organizations a sharper, faster view of emerging risks. With deeper, more actionable intelligence at their fingertips, security teams can outpace threat actors, respond instantly to Zero-Day attacks, and dramatically shrink their risk exposure window.
Identify exposed access points, detect misconfigured SSL certificates, and uncover vulnerabilities across the network infrastructure.
Gain visibility into the software components used within an organization to detect vulnerabilities, manage risk, and ensure supply chain security.
Monitor and manage all IT assets and their configurations to ensure accurate, real-time visibility across the company's technology environment.
Leverage real-time insights on active threats, malware campaigns, and emerging vulnerabilities to proactively defend against evolving cyberattacks.




