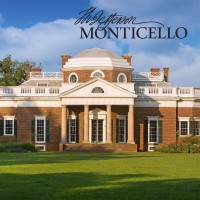
Thomas Jefferson Foundation
The Thomas Jefferson Foundation (formerly the Thomas Jefferson Memorial Foundation) owns and operates Monticello, the mountaintop home of Thomas Jefferson and the only home in America on the elite World Heritage List of the United Nations. Incorporated in 1923, after the federal government waived its third opportunity to acquire Monticello for the nation, the Foundation purchased the house and land from the Levy family, stewards of the estate for 89 years. As a private, nonprofit organization, the Foundation receives no regular federal or state budget support for its twofold mission of preservation and education. Since 1923, the Thomas Jefferson Foundation has steadily expanded its role as a museum and educational institution. Its facilities now include the house and gardens on nearly 2,000 of Jefferson's original 5,000 acres; the Robert H. Smith International Center for Jefferson Studies next door at Kenwood, a headquarters for Jeffersonian research and teaching and home to the Jefferson Library; and the Thomas Jefferson Center for Historic Plants, which propagates heirloom varieties and makes them available to institutions and individuals. The David M. Rubenstein Visitor Center and Smith Education Center hosts state-of-the art exhibits for visitors of all ages. It serves as the gateway to Jefferson’s timeless Monticello, preparing guests for their trips to the historic mountaintop through dynamic content presenting fresh perspectives on Monticello and the enduring significance of Jefferson’s life and ideas. About a half a million people visit Monticello each year.






