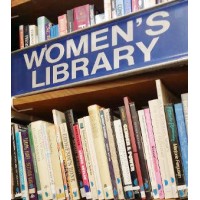
The Women's Library, Sydney
The Women's Library is a specialist lending library and community space in inner Sydney, Australia. This community-based library with its collection of books for, by, and about women, is a hub of feminist and lesbian activity. The Women's Library has been built on the efforts of volunteers and the donations of thousands of women since its establishment in 1992. It is fully managed and staffed by volunteers and the collection of donated books, journals, and DVDs numbers approximately 20,000 items. Annual membership is open to women and women's groups that support the library's aims. The Women's Library gratefully acknowledges the support of the City of Sydney.






