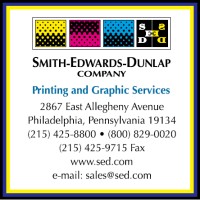
Smith-Edwards-Dunlap Company
Diverse Clients. Diverse Needs. One Dynamic Solution. As Philadelphia’s leading commercial printing company, Smith-Edwards-Dunlap (SED) has built a reputation of achieving high levels of client satisfaction through exceptional service and high quality commercial printing production. What sets us apart from other commercial printing companies is our ability to integrate century-old values and traditions with continually evolving modern technology and exceptional customer service. In fact, we are so obsessed with meeting and exceeding expectations that we tailor our commercial printing process to each job and then execute with the efficiency that clients can rely on. Smith-Edwards-Dunlap’s tradition is a promise to exceed client expectation through loyalty and dedication. The commitment to printing technology, combined with relentless care in execution, is how Smith-Edwards-Dunlap satisfies that promise.






