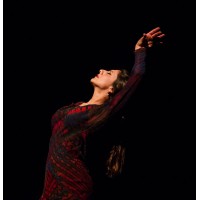
Omayra Amaya Flamenco Dance Company, Inc.
The Omayra Amaya Flamenco Dance Company is a nonprofit performing arts organization dedicated to the advancement and awareness of flamenco dance and music. We strive to increase understanding and appreciation for this dynamic Spanish art form through performances, education, and presence in communities around the world. About Omayra Amaya Omayra Amaya is modern flamenco dancer and choreographer deeply rooted in proud gypsy tradition. The daughter of flamenco dancers Olga and Curro Amaya and grandniece of the legendary Carmen Amaya, Omayra brings new relevance to flamenco while never losing sight of her legacy.






