Ohr-O'Keefe Museum of Art
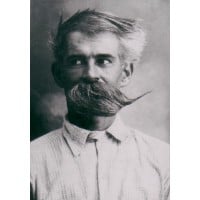
The mission of the Ohr-O’Keefe Museum of Art is to promote and preserve the unique legacy of Biloxi potter George E. Ohr and the diverse cultural heritage of the Mississippi Gulf Coast; and to exhibit works which exemplify the independent, innovative, and creative spirit of George Ohr, emancipated craftsman Pleasant Reed, and Ohr-O’Keefe Museum architect Frank Gehry. This mission is served through compelling exhibitions and educational experiences viewed from a fresh perspective relevant to our community, the region, and the nation with a strong focus on ceramic arts.






