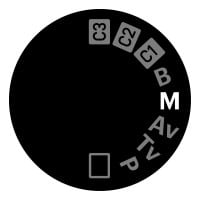
Manual
Manual: Shaping and amplifying world-changing ideas. We are a team of curious designers, communicators, and thinkers driven by the belief that bold creativity can positively shape society and culture. From our studios in San Francisco and Amsterdam, we partner with visionary clients—big and small—who challenge conventions and inspire meaningful change. We develop strategies and design experiences that empower businesses and organizations to create lasting impact and move the world forward.






