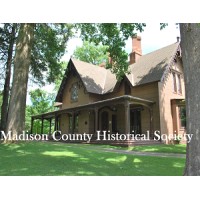
Madison County Historical Society
Madison County Historical Society, is a 501 (c) 3 non-profit educational institution chartered by the New York State Board of Regents on March 29, 1900. The Madison County Historical Society’s mission is to preserve, collect, promote, and exhibit the history of Madison County and its fifteen towns and one city through the development of programs that enhance the county’s heritage for the people of Madison County and those studying the county’s heritage. The society’s headquarters, Cottage Lawn, is an 1849 Gothic Revival Villa designed by prominent architect Alexander Jackson Davis. Cottage Lawn is preserved and operated as a historic museum. Madison County Historical Society welcomes visitors to home of banker Niles Higinbotham. Construction of the residence, named Cottage Lawn, commenced in 1849 and was completed in September of 1850 upon the birth of Niles and Eliza Higinbotham’s first daughter, Julia. Mrs. Eliza Higinbotham and two of her three daughters, Lily and Louise, were among the 64 MCHS charter members that established the Madison County Historical Society. The society’s first meeting was held on April 20, 1898.The society adopted its articles of incorporation on October 19, 1898 and received its charter from the New York State Board of Regents on March 29, 1900. On June 15, 1934 the society officially opened. By 1984, it was placed on the State and National Register of Historic Places for its outstanding Gothic Revival Architecture. The society’s museum is open to the public for guided tours year round. The society operates the Mary King Genealogical Research Library named after Mary King in 2002 for her twenty-two years of volunteer service helping families with their genealogy. Throughout the year a variety of special events and educational programs are offered. Annual events sponsored by the society include Madison County Craft Festival, Madison County Hop Fest, Cottage Lawn Farmers’ Market, and Victorian Christmas Open House.






