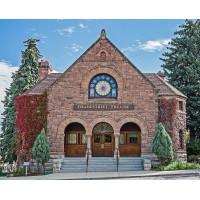
Grandstreet Theatre
Grandstreet Theatre is a community-powered Montana institution that produces 8-10 shows each year. We have a 200-seat house in a beautiful turn-of-the-century Romanesque granite church. Our 35-year-old education program boasts an enrollment of over 350 students. Nestled at the base of the Rocky Mountains in a small but thriving arts community, Grandstreet enjoys tremendous public support and is consistently producing some of the best theatre in the Northwest.






