ESSENTIAL PUBLICATIONS U.S. LLC
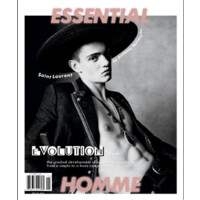
Essential Publications U.S. LLC is a magazine publishing company based in New York City, USA. It currently publishes Essential Homme - Men's Fashion & Style. Essential Homme is distributed nationally in U.S./Canada as well as Internationally (Europe, Asia, Australia, Mexico, UAE, Canada etc.). About Essential Homme Magazine: Essential Homme is the style source for affluent, successful, and fashion-forward men who are passionate about high quality, high-end luxury fashion.