EmmaWell
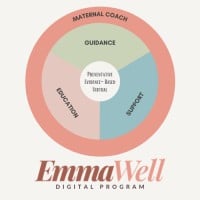
EmmaWell partners with payers, employers, and healthcare providers who want to take a proactive approach to help pregnant people and new parents who screen at risk for a perinatal mental health condition. Our comprehensive digital program spans the pregnancy and postpartum journey and is designed to help manage existing symptoms of anxiety and mood disorders and ultimately prevent postpartum depression. The EmmaWell program includes unlimited access to a maternal coach along with personalized mental health support, guidance, and education from the start of your pregnancy through three months postpartum. For more information, please reach out to us at [email protected].






