Royal Family Productions, Inc.
145 W 46th St, New York, NY, 10036, US
Last Update: 2025-12-11
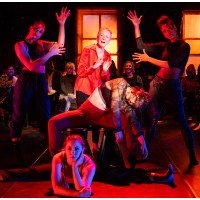
Royal Family’s mission is to galvanize the Times Square community by cultivating raw talent, collaborating with seasoned artists, and inspiring audiences with a diversity of lion-hearted theatre. To us, everyone in the theatre community is not only royalty, but family. Our programs and productions lift artists at all stages of their careers. In today’s political and social climate, we continue to celebrate all voices—especially those underrepresented in the traditional theatre space. Royal Family celebrates the work of female artists, playwrights of color, works with LGBTQIA themes, and artists of all ages and body types. Royal Family has been a creative incubator of original, humanistic plays for over a decade. Bravery and fearlessness are imperative to our process. Artists and audiences alike are challenged in a creative safe space to explore the humor and the tangled truths of the human condition. As actor and first-time playwright Anthony Rapp (Rent, Dazed and Confused, Star Trek: Discovery, If/Only, Without You) observes, “Royal Family is committed to truthful, heartfelt, alive, theatrical storytelling. It’s vital to the human experience and hard to come by.” Royal Family achieves its mission through the following objectives: Launching the careers of emerging artists by pairing them with established professionals, pushing them with ferocious care to make their project the best it can be; Championing artists in all stages of play development, from the kernel of an idea and blossoming it into a reading, workshop, or a full-scale production that introduces emerging artists to the theatre community or showcases established professionals who are experimenting with different facets of their artistry; Activating audiences in the artistic process through first-draft readings and workshop feedback, alternative show times, and shorter run times; Presenting visceral theatre experiences that push the boundaries of creative expression.
NAICS: 711
NAICS Definition:
Employees: 22
Subsidiaries: 0